Zero Trust Security Market Size, Share, Growth | Report 2030
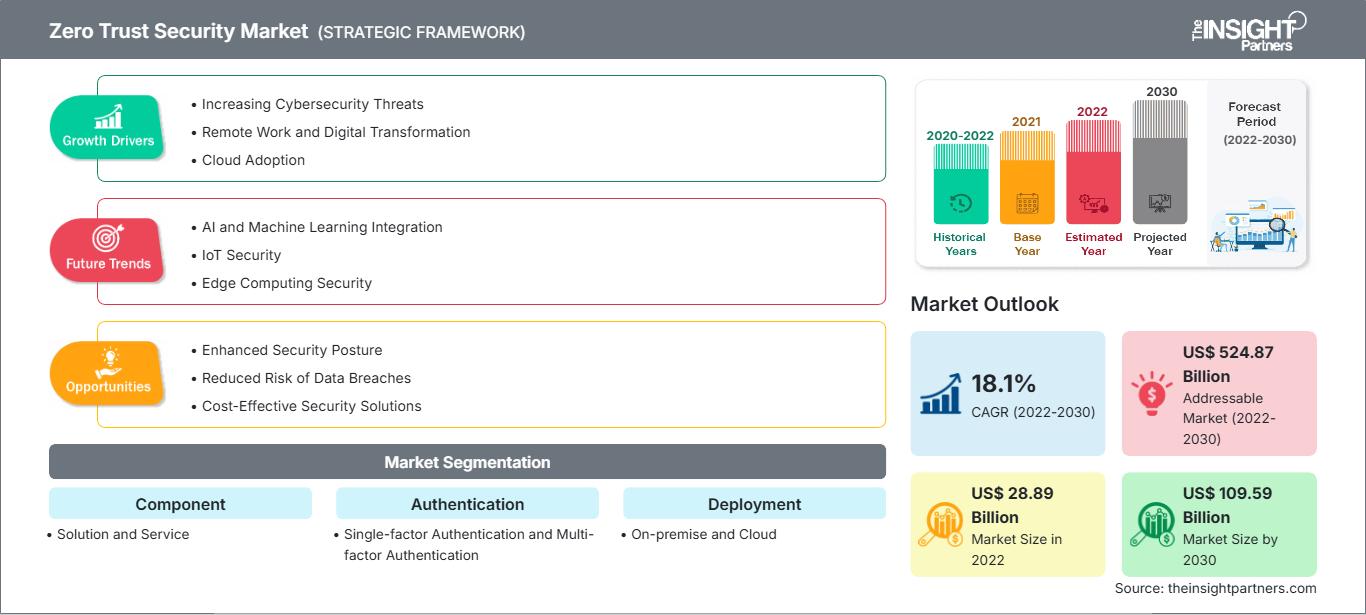
Zero Trust Security Market Size and Forecasts (2020 - 2030), Global and Regional Share, Trends, and Growth Opportunity Analysis Report Coverage: By Component (Solution and Service), Authentication (Single-factor Authentication and Multi-factor Authentication), Deployment (On-premise and Cloud), Organization Size (SMEs and Large Enterprises), Application (Endpoint, Network, and Others), and End Use (BFSI, E-commerce & Retail, Healthcare, IT & Telecom, and Others)
Historic Data: 2020-2022 | Base Year: 2022 | Forecast Period: 2022-2030- Status : Data Released
- Report Code : TIPRE00008893
- Category : Technology, Media and Telecommunications
- No. of Pages : 150
- Available Report Formats :


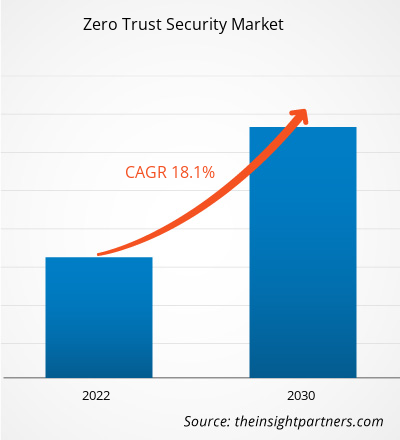
[Research Report] The zero trust security market size was valued at US$ 28.89 billion in 2022 and is expected to reach US$ 109.59 billion by 2030; it is estimated to record a CAGR of 18.1% from 2022 to 2030.
Zero Trust Security Market Analyst Perspective:
Identity and access management (IAM) is a crucial element of a zero trust security approach, as it aids organizations in ensuring that unauthorized users do not have access to sensitive resources. By deploying IAM systems, corporations can establish and impose policies for determining which person has access to what resources and can incessantly verify the identity of users and devices to safeguard security and ensure that they are approved to access specific resources. In addition, IAM systems can assist enterprises in tracking user access to resources and detect when unauthorized access or illegitimate activity is attempted. This can aid organizations in identifying and inhibiting probable security breaches; thus, it is an important asset for complying with regulatory requirements related to data privacy and security. Thus, with the appropriate IAM solution, corporations can establish zero trust authentication and authorization methods, as well as zero trust encryption for in-transit and at-rest data.
Zero Trust Security Market Overview:
The global zero trust security market is experiencing extensive growth and is estimated to continue expanding in the coming years. Zero trust is a framework that ensures the security of the infrastructure and data of an enterprise. It exclusively addresses the contemporary challenges of present-day business, including securing hybrid cloud environments, remote workers, and ransomware threats. The zero trust security market is moderately fragmented. Market players are expanding their business by employing various methods, such as product portfolio expansion, service expansion, mergers & acquisitions (M&A), and collaborations. In June 2023, AKITA, a leading technology zero trust and network security solutions provider, merged with odixa—a major provider of advanced malware prevention solutions. The merger is anticipated to enable the new company to offer advanced and comprehensive zero trust cybersecurity solutions to their clientele.
Customize This Report To Suit Your Requirement
Get FREE CUSTOMIZATIONZero Trust Security Market: Strategic Insights
-
Get Top Key Market Trends of this report.This FREE sample will include data analysis, ranging from market trends to estimates and forecasts.
Zero Trust Security Market Driver:
Rise in Bring Your Own Device (BYOD) Fuels Zero Trust Security Market Growth
Many well-known data experts agree that the generated data will grow exponentially during the forecast period. Based on research from Seagate's Data Age 2025 report, the world's data sphere will reach 175 zettabytes by 2025. This development is attributed to the enormous increase in people working, studying, and using streaming platforms from home. Hence, such a change is expected to create lucrative opportunities for the zero trust security market players over the forecast period. Additionally, the IT infrastructure is expected to become more complicated and varied due to the Bring Your Own Device (BYOD) regulations, utilization of business apps, introduction of new platforms, Choose Your Own Device (CYOD) trends, and implementation of other technologies. The BYOD and CYOD trends are becoming increasingly common in business settings due to the rapid improvements in mobile computing. Hence, employees are able to access organizational data via mobile devices anytime, which increases employee productivity. Installation of zero trust solutions, for such instances, ensures that organizational data is secured and kept confidential. Such factors are strongly fueling the demand for solutions and services offered by the zero trust security market players.
Zero Trust Security Market Segmental Analysis:
The zero trust security market is categorized on the basis of component, authentication, deployment, organization size, application, and end use. Based on component, the zero trust security market is bifurcated into solution and service. In terms of authentication, the market is divided into single-factor authentication and multi-factor authentication. Based on deployment, the market is bifurcated into on-premise and cloud. Based on organization size, the market is bifurcated into SMEs and large enterprises. In terms of application, the market is segmented into endpoint, network, and others. Based on end use, the market is segmented into BFSI, e-commerce & retail, healthcare, IT & telecom, and others. By geography, the zero trust security market is segmented into North America, Europe, Asia Pacific (APAC), the Middle East & Africa (MEA), and South America (SAM).
Single-factor authentication simplifies zero-trust authentication by allowing users to access multiple resources and systems with a single set of credentials rather than requiring different login information for each system. It can enhance the user experience and reduce the risk of users choosing weak passwords, as well as diminish the risk of users recycling passwords across multiple systems. Multi-factor authentication might seem cumbersome to the user, but it is deemed more secure. By mandating multiple authentication factors, it aids organizations to ensure that only approved users can avail sensitive resources by making it harder for attackers to gain illicit access, even if they are succesful in obtaining a user’s password. It is often used in conjunction with other zero trust solutions, such as IAM systems, to provide an added layer of security.
Zero Trust Security Market Regional Analysis:
The development of data protection and cybersecurity laws in Asian countries is expanding significantly. As individuals become occupied in new digital reality via mobile handsets and the internet-of-things (IoT), there is an increase in government iniatiatives toward digital identity programs and invasive approaches to electronic surveillance. In this respect, the use of the General Data Protection Regulation (GDPR) and data protection rules in the region is gaining attention. For instance, the region has experienced significant steps in China. APAC is presumed to emerge as the fastest-growing region over the forecast period. The growing acceptance of mobile devices across businesses and IoT applications is primarily responsible for the market growth in the region. Furthermore, the growing adoption of bring your own device (BYOD) policies and cloud-based solutions is another factor contributing to the zero trust security market growth. Additionally, the growth in digital workplace trends and transformation in data centers is anticipated to boost zero trust security market growth over the forecast period.
Zero Trust Security Market Report Scope
| Report Attribute | Details |
|---|---|
| Market size in 2022 | US$ 28.89 Billion |
| Market Size by 2030 | US$ 109.59 Billion |
| Global CAGR (2022 - 2030) | 18.1% |
| Historical Data | 2020-2022 |
| Forecast period | 2022-2030 |
| Segments Covered |
By Component
|
| Regions and Countries Covered |
North America
|
| Market leaders and key company profiles |
|
Zero Trust Security Market Players Density: Understanding Its Impact on Business Dynamics
The Zero Trust Security Market is growing rapidly, driven by increasing end-user demand due to factors such as evolving consumer preferences, technological advancements, and greater awareness of the product's benefits. As demand rises, businesses are expanding their offerings, innovating to meet consumer needs, and capitalizing on emerging trends, which further fuels market growth.
Zero Trust Security Market Key Player Analysis:
Akamai Technologies Inc, Cato Networks Ltd, Check Point Software Technologies Ltd, Cisco Systems Inc, Fortinet Inc, Microsoft Corporation, Okta Inc, Palo Alto Networks Inc, VMWare Inc, and Zscaler Inc are among the key zero trust security market players operating in the market. Several other major companies have been analyzed during this research study to get a holistic view of the zero trust security market ecosystem.
Zero Trust Security Market Recent Developments:
The zero trust security market players highly adopt inorganic and organic strategies. A few major zero trust security market developments are listed below:
- In August 2023, Check Point Software, a leading cybersecurity company, announced the acquisition of secure access service edge (SASE) and network security vendor, Perimeter 81, for US$ 490 million to enhance its offerings for security beyond the network perimeter. The former company plans to integrate the latter’s zero trust network access and rapid deployment technology into its existing Infinity product architecture.
- In March 2023, Hewlett Packard Enterprise announced its plan to acquire Israeli cyber startup, Axis Security. The latter company offers cloud-based Security Services Edge (SSE) solutions that enable access to corporate and public cloud resources.
Frequently Asked Questions
Ankita is a dynamic market research and consulting professional with over 8 years of experience across the technology, media, ICT, and electronics & semiconductor sectors. She has successfully led and delivered 100+ consulting and research assignments for global clients such as Microsoft, Oracle, NEC Corporation, SAP, KPMG, and Expeditors International. Her core competencies include market assessment, data analysis, forecasting, strategy formulation, competitive intelligence, and report writing.
Ankita is adept at handling complete project cycles—from pre-sales proposal design and client discussions to post-sales delivery of actionable insights. She is skilled in managing cross-functional teams, structuring complex research modules, and aligning solutions with client-specific business goals. Her excellent communication, leadership, and presentation abilities have enabled her to consistently deliver value-driven outcomes in fast-paced and evolving market environments.
- Historical Analysis (2 Years), Base Year, Forecast (7 Years) with CAGR
- PEST and SWOT Analysis
- Market Size Value / Volume - Global, Regional, Country
- Industry and Competitive Landscape
- Excel Dataset
Testimonials
The Insight Partners' SCADA System Market report is comprehensive, with valuable insights on current trends and future forecasts. The team was highly professional, responsive, and supportive throughout. We are very satisfied and highly recommend their services.
RAN KEDEM Partner, Reali Technologies LTDsI requested a report on a very specific software market and the team produced the report in a few days. The information was very relevant and well presented. I then requested some changes and additions to the report. The team was again very responsive and I got the final report in less than a week.
JEAN-HERVE JENN Chairman, Future AnalyticaWe worked with The Insight Partners for an important market study and forecast. They gave us clear insights into opportunities and risks, which helped shape our plans. Their research was easy to use and based on solid data. It helped us make smart, confident decisions. We highly recommend them.
PIYUSH NAGPAL Sr. Vice President, High Beam GlobalThe Insight Partners delivered insightful, well-structured market research with strong domain expertise. Their team was professional and responsive throughout. The user-friendly website made accessing industry reports seamless. We highly recommend them for reliable, high-quality research services
YUKIHIKO ADACHI CEO, Deep Blue, LLC.This is the first time I have purchased a market report from The Insight Partners.While I was unsure at first, I visited their web site and felt more comfortable to take the risk and purchase a market report.I am completely satisfied with the quality of the report and customer service. I had several questions and comments with the initial report, but after a couple of dialogs over email with their analyst I believe I have a report that I can use as input to our strategic planning process.Thank you so much for taking the extra time and making this a positive experience.I will definitely recommend your service to others and you will be my first call when we need further market data.
JOHN SUZUKI President and Chief Executive Officer, Board Director, BK TechnologiesI wish to appreciate your support and the professionalism you displayed in the course of attending to my request for information regarding to infectious disease IVD market in Nigeria. I appreciate your patience, your guidance, and the fact that you were willing to offer a discount, which eventually made it possible for us to close a deal. I look forward to engaging The Insight Partners in the future, all thanks to the impression you have created in me as a result of this first encounter.
DR CHIJIOKE ONYIA MANAGING DIRECTOR, PineCrest Healthcare Ltd.Reason to Buy
- Informed Decision-Making
- Understanding Market Dynamics
- Competitive Analysis
- Identifying Emerging Markets
- Customer Insights
- Market Forecasts
- Risk Mitigation
- Boosting Operational Efficiency
- Strategic Planning
- Investment Justification
- Tracking Industry Innovations
- Aligning with Regulatory Trends





 Get Free Sample For
Get Free Sample For