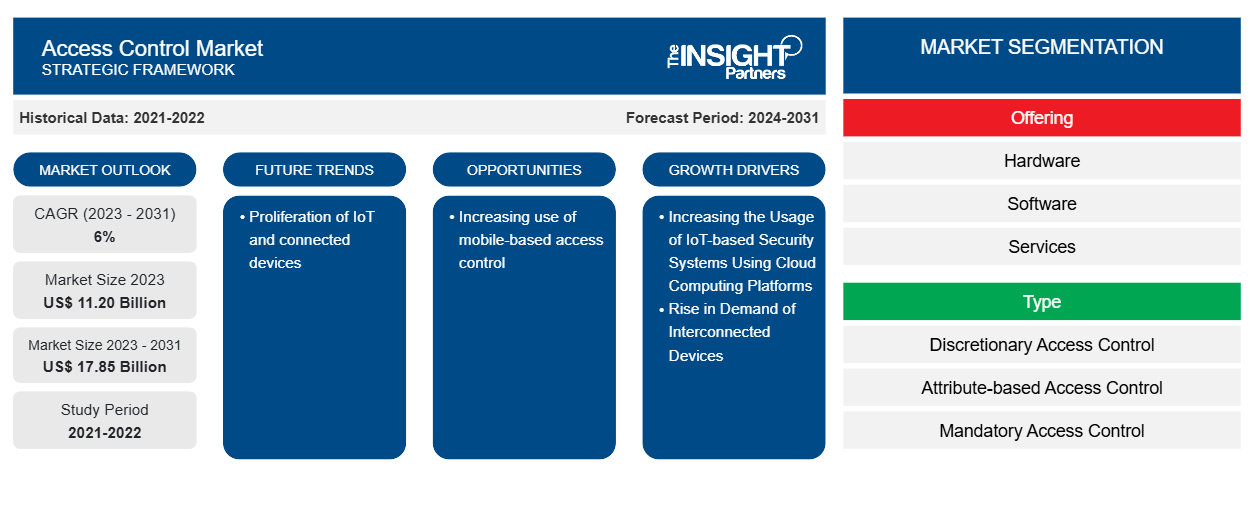
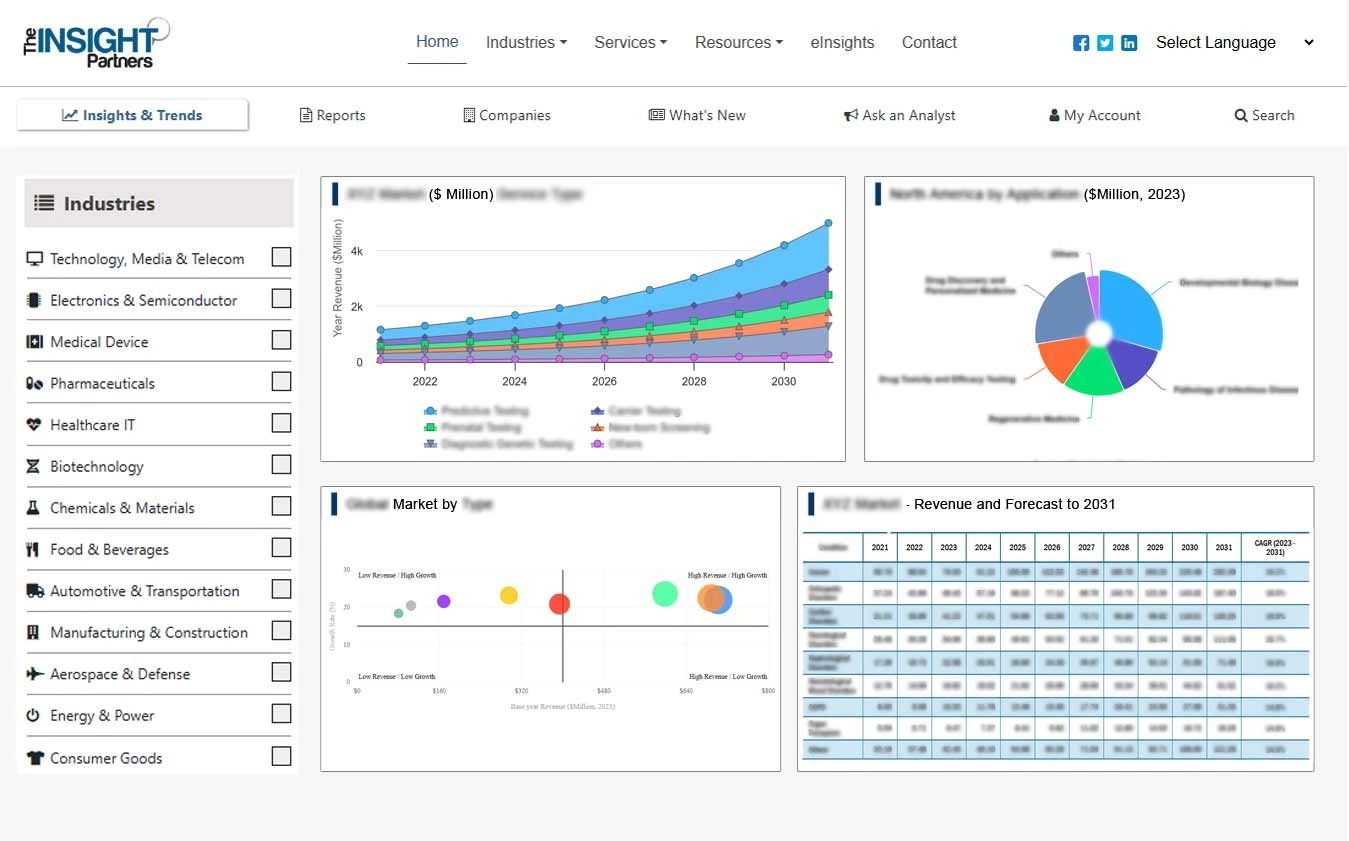
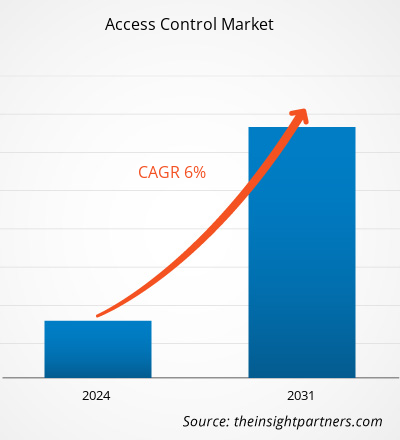
The access control market size is projected to reach US$ 17.85 billion by 2031 from US$ $ 11.20 billion in 2023. The access control market is expected to register a CAGR of 6% in 2023–2031. The market is expanding because of the growing demand for stronger security systems as well as widespread usage of the Internet of Things (IoT) and cloud computing platforms.
Access Control Market Analysis
Access control protects confidential information, such as customer data and intellectual property, from theft by malicious actors or other unauthorized users. It also decreases the danger of employee data exfiltration and protects against web-based threats. Rather than manually managing permissions, most security-conscious firms rely on identity and access management technologies to enforce access controls.
Access Control Market Overview
Access control is a security strategy that governs who or what can view or utilize resources in a computer environment. It is a core security concept that reduces risk to the company or organization. Access control is a critical component of security that governs who has access to specific data, apps, and resources—and under what conditions. Keys and preapproved visitor lists secure physical facilities, much as access control protocols do for digital spaces. In other words, they allow the right people in while keeping the bad people out. Access control policies rely heavily on techniques such as authentication and authorization, which enable organizations to explicitly verify that users are who they claim to be and that these users have the appropriate level of access based on context, such as device, location, role, and much more.
Customize This Report To Suit Your Requirement
You will get customization on any report - free of charge - including parts of this report, or country-level analysis, Excel Data pack, as well as avail great offers and discounts for start-ups & universities
Access Control Market: Strategic Insights
- Get Top Key Market Trends of this report.This FREE sample will include data analysis, ranging from market trends to estimates and forecasts.
You will get customization on any report - free of charge - including parts of this report, or country-level analysis, Excel Data pack, as well as avail great offers and discounts for start-ups & universities
Access Control Market: Strategic Insights
- Get Top Key Market Trends of this report.This FREE sample will include data analysis, ranging from market trends to estimates and forecasts.
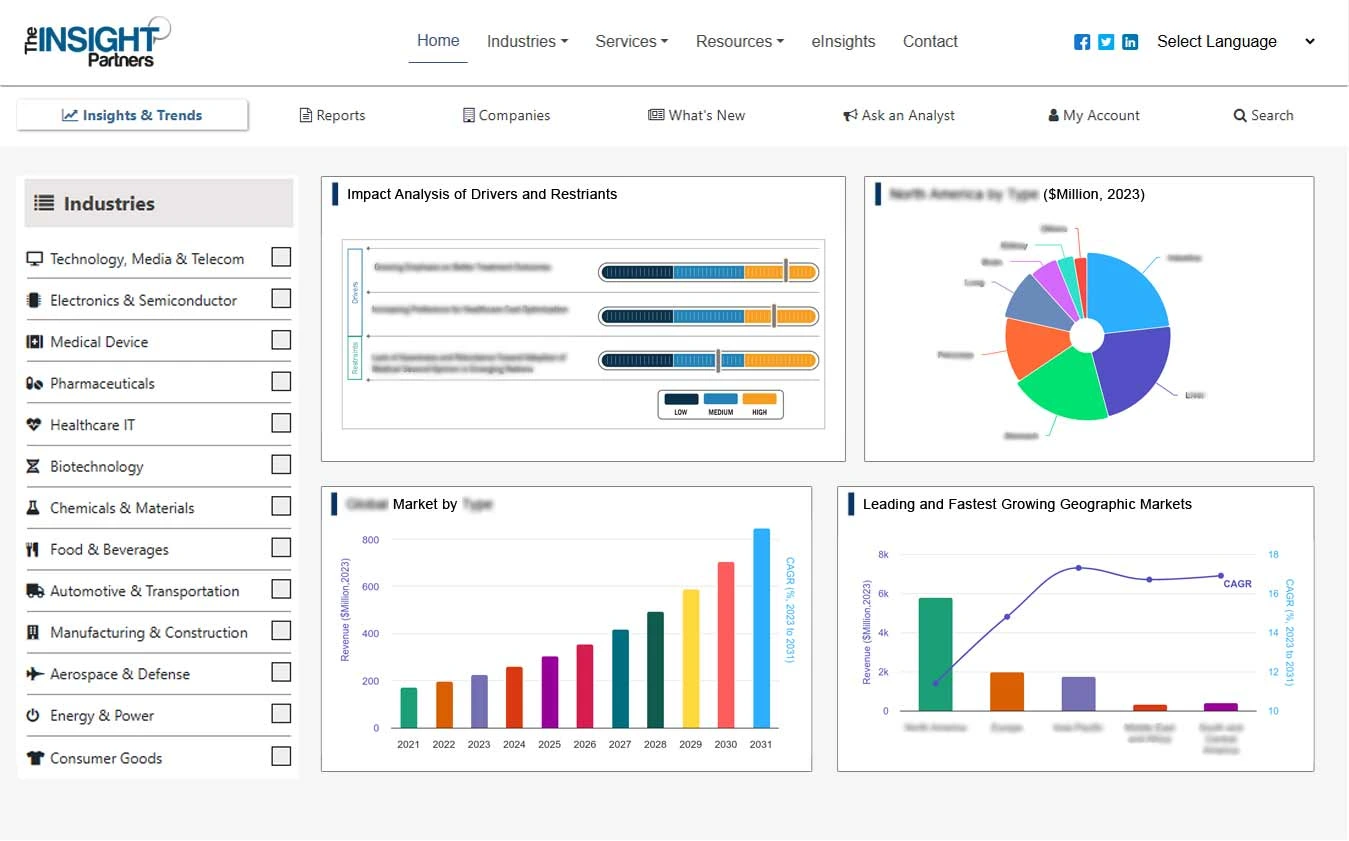
Access Control Market Drivers and Opportunities
Increasing the Usage of IoT-based Security Systems Using Cloud Computing Platforms to Favor Market
The rise of IoT-based security solutions and cloud computing is fueling demand for access control. Traditional access control systems, as opposed to cloud-based access control systems, frequently have restrictions and complications that might undermine their usefulness. With the introduction of IoT cloud-based access control systems, organizations now have access to cutting-edge solutions that provide unsurpassed security and convenience. Cloud-based IoT access control systems provide effortless integration with various hardware and infrastructure components. Whether it's facial recognition, RFID, QR codes, mobile access, keypad entry, or fingerprint scanning, these systems offer multiple options to meet various security needs. Due to this, the IoT-based security solution using cloud computing is growing. Increasing the usage of IoT-based security systems using cloud computing platforms is driving the growth of the access control market.
Increasing use of mobile-based access control
Mobile access control utilizes smartphones, tablets, and wearable electronic devices and allows them to function as a user's credentials to enter offices or other business premises. Mobile access control offers a wide range of benefits, but the enhanced security and ease of use set it apart. Unlike physical cards and fobs that are easy to lose, mobile credentials are stored on an employee’s phone, making them easier to keep track of — and less likely to fall into the wrong hands. Mobile credentials are an authentication method that is stored in a mobile device; these credentials are verified by an individual. Each mobile credential is unique to an individual, and the credentials are encrypted to safeguard the identity of users. Due to the above benefits the use of mobile-based access control is increasing, creating opportunity for the growth of the access control market.
Access Control Market Report Segmentation Analysis
Key segments that contributed to the derivation of the access control market analysis are component, offering, type, and end user.
- Based on the offering, the access control market is divided into hardware, software, and services.
- By type, the market is segmented into discretionary access control (DAC), attribute-based access control (ABAC), mandatory access control (MAC), role-based access control (RBAC), and others.
- Based on end users, the access control market is divided into residential, commercial, industrial, and homeland security.
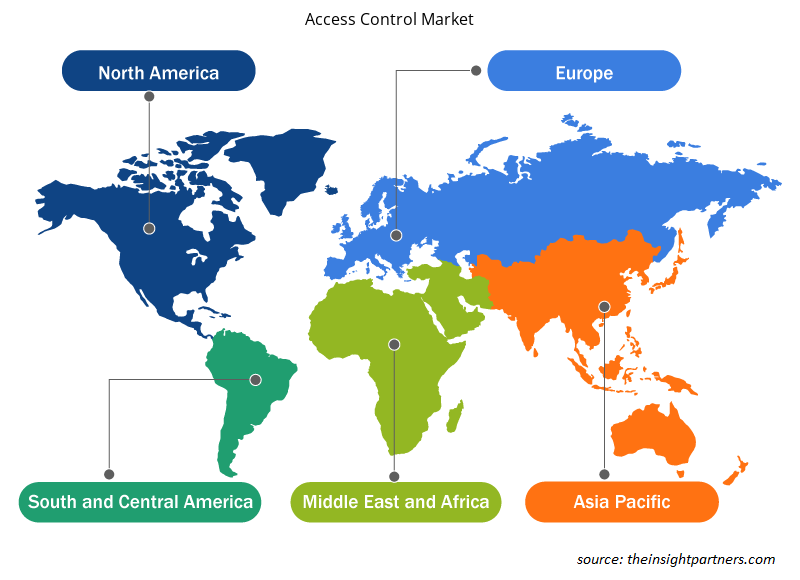
Access Control Market Share Analysis by Geography
The geographic scope of the access control market report is mainly divided into five regions: North America, Asia Pacific, Europe, Middle East & Africa, and South America/South & Central America. Asia Pacific has dominated the access control market. China continues to dominate the Asia-Pacific market, thanks mostly to its developing construction sector, a significant number of manufacturing enterprises, and rising crime rates. The deployment of mobile-based access control solutions is also increasing throughout the country. China's smart door lock market has expanded rapidly in recent years, owing to advances in biometric identification and wireless communication technology. In Japan, the government and businesses have shown a strong interest in the security aspects of access control solutions, resulting in the implementation of new legislation, strategies, and facilities. Japanese firms are aggressively studying and developing newer biometric and authentication technologies that provide a touchless experience.
Access Control Market Regional Insights
The regional trends and factors influencing the Access Control Market throughout the forecast period have been thoroughly explained by the analysts at Insight Partners. This section also discusses Access Control Market segments and geography across North America, Europe, Asia Pacific, Middle East and Africa, and South and Central America.
- Get the Regional Specific Data for Access Control Market
Access Control Market Report Scope
| Report Attribute | Details |
|---|---|
| Market size in 2023 | US$ 11.20 Billion |
| Market Size by 2031 | US$ 17.85 Billion |
| Global CAGR (2023 - 2031) | 6% |
| Historical Data | 2021-2022 |
| Forecast period | 2024-2031 |
| Segments Covered |
By Offering
|
| Regions and Countries Covered | North America
|
| Market leaders and key company profiles |
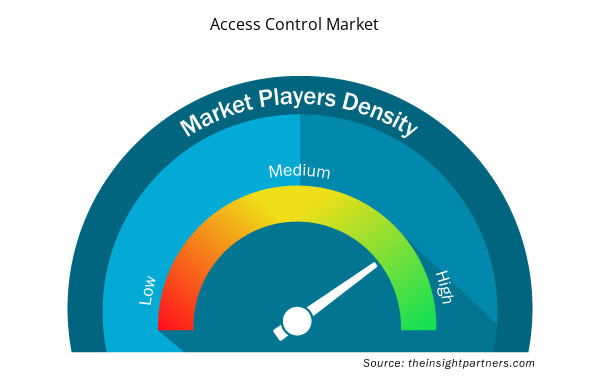
Access Control Market Players Density: Understanding Its Impact on Business Dynamics
The Access Control Market is growing rapidly, driven by increasing end-user demand due to factors such as evolving consumer preferences, technological advancements, and greater awareness of the product's benefits. As demand rises, businesses are expanding their offerings, innovating to meet consumer needs, and capitalizing on emerging trends, which further fuels market growth.
Market players density refers to the distribution of firms or companies operating within a particular market or industry. It indicates how many competitors (market players) are present in a given market space relative to its size or total market value.
Major Companies operating in the Access Control Market are:
- Honeywell International Inc.
- dormakaba Group
- ASSA ABLOY
- Johnson Controls
- Allegion Plc.
- Nedap N.V.
Disclaimer: The companies listed above are not ranked in any particular order.
- Get the Access Control Market top key players overview
Access Control Market News and Recent Developments
The access control market is evaluated by gathering qualitative and quantitative data post primary and secondary research, which includes important corporate publications, association data, and databases. The following is a list of developments in the market:
- In October 2022, - ASSA ABLOY AB finalized the acquisition of ALCEA, a French access control solutions provider. ALCEA will be integrated into ASSA ABLOY's Critical Infrastructure business portfolio, allowing the company to strengthen its presence in critical infrastructure protection contexts while also expanding its product access-focused product line. This acquisition aligns with the company's strategic ambition to strengthen its position in the access control sector.
(Source: ASSA ABLOY AB, Press Release, 2023)
- In March 2023, Axis Communications and Genetec Inc. collaborated to create Axis, an enterprise-level access control system that integrates Genetec access control software and Axis network door controllers into a single, simple-to-install package. This is the first of its kind on the market, combining Genetec technology to give comprehensive security, public safety, operations, and business intelligence solutions.
(Source: Axis Communications, Press Release, 2023)
Access Control Market Report Coverage and Deliverables
The "Access Control Market Size and Forecast (2023–2031)" report provides a detailed analysis of the market covering below areas:
- Market size and forecast at global, regional, and country levels for all the key market segments covered under the scope
- Market dynamics such as drivers, restraints, and key opportunities
- Key future trends
- Detailed PEST/Porter's Five Forces and SWOT analysis
- Global and regional market analysis covering key market trends, major players, regulations, and recent market developments
- Industry landscape and competition analysis covering market concentration, heat map analysis, prominent players, and recent developments
- Detailed company profiles
- Historical Analysis (2 Years), Base Year, Forecast (7 Years) with CAGR
- PEST and SWOT Analysis
- Market Size Value / Volume - Global, Regional, Country
- Industry and Competitive Landscape
- Excel Dataset
Report Coverage
Revenue forecast, Company Analysis, Industry landscape, Growth factors, and Trends
Segment Covered
Type and Application
Regional Scope
North America, Europe, Asia Pacific, Middle East & Africa, South & Central America
Country Scope
US, Canada, Mexico, UK, Germany, Spain, Italy, France, India, China, Japan, South Korea, Australia, UAE, Saudi Arabia, South Africa, Brazil, Argentina
Frequently Asked Questions
What is the estimated market size for the global access control market in 2023?
The global access control market was estimated to be US$ 11.20 billion in 2023 and is expected to grow at a CAGR of 6.8% during the forecast period 2023 - 2031.
What are the driving factors impacting the global access control market?
Increasing the usage of IoT-based security systems using cloud computing platforms is the major factors that propel the global access control market.
What will be the market size of the global access control market by 2031?
The global access control market is expected to reach US$ 17.85 billion by 2031.
Which are the key players holding the major market share of the access control market?
The key players holding majority shares in the global access control market are Honeywell International Inc., dormakaba Group, ASSA ABLOY, Johnson Controls, and Allegion Plc.
What are the future trends of the Global access control market?
The proliferation of IoT and connected devices is anticipated to play a significant role in the global access control market in the coming years.
 Get Free Sample For
Get Free Sample For