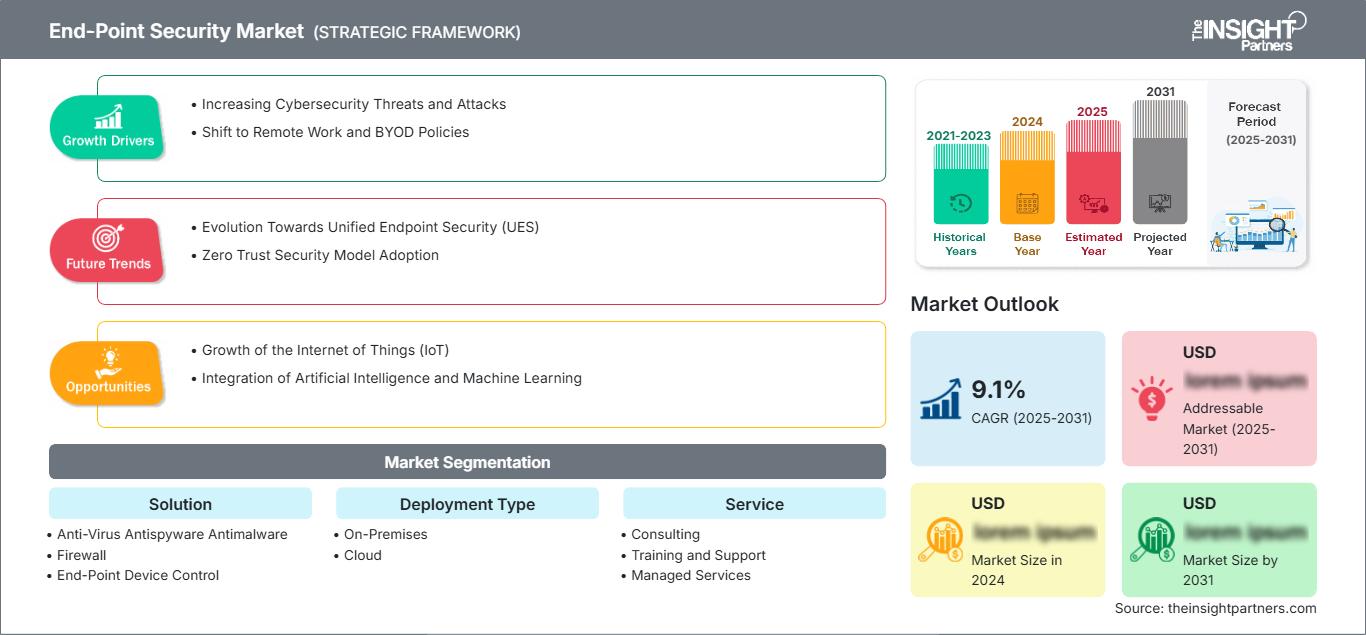
Endpoint Security Market Revenue Growth, Market Trends, and Competitive Landscape by 2031
Endpoint Security Market Size and Forecast (2021 - 2031), Global and Regional Share, Trend, and Growth Opportunity Analysis Report Coverage: By Component (Solution and Services), Organization Size (Large Enterprises and SMEs), Industry Vertical (BFSI, IT and Telecom, Government, Healthcare, Manufacturing, Retail and Ecommerce, and Others), and Geography (North America, Europe, Asia Pacific, Middle East and Africa, and South and Central America)
Historic Data: 2021-2023 | Base Year: 2024 | Forecast Period: 2025-2031- Report Code : TIPRE00003398
- Category : Technology, Media and Telecommunications
- No. of Pages : 293
- Available Report Formats :


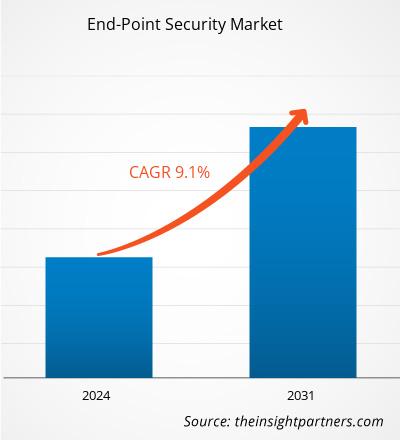
The endpoint security market size is expected to reach US$ 144.95 billion by 2031 from US$ 58.22 billion in 2024. The market is anticipated to register a CAGR of 14.2% during 2025–2031.
Endpoint Security Market Analysis
The endpoint security market is growing due to rising cyber threats, remote work adoption, and cloud usage. Organizations demand advanced protection, driving innovation in AI-based detection, zero trust models, and integrated security platforms worldwide.
Endpoint Security Market Overview
The endpoint security market focuses on protecting devices from cyber threats, driven by remote work, cloud adoption, regulatory pressure, and demand for advanced threat detection and response solutions worldwide.
Customize This Report To Suit Your Requirement
Get FREE CUSTOMIZATIONEndpoint Security Market: Strategic Insights
-
Get Top Key Market Trends of this report.This FREE sample will include data analysis, ranging from market trends to estimates and forecasts.
Endpoint Security Market Drivers and Opportunities
Market Drivers:
- Rising Cyber Threats: Increasing malware, ransomware, and phishing attacks push organizations to adopt robust endpoint security.
- Remote Work Adoption: Widespread remote work increases vulnerability, creating demand for secure endpoint solutions.
- Cloud and IoT Growth: More connected devices and cloud usage expand attack surfaces, necessitating endpoint protection.
- Regulatory compliance: Data protection laws (such as GDPR) force businesses to implement strong endpoint security.
- Advanced Persistent Threats (APTs): Sophisticated attacks require AI-driven detection and proactive security measures.
Market Opportunities:
- AI and Machine Learning Integration: Enhancing threat detection and response through predictive analytics and automation.
- Zero Trust Security Adoption: Providing secure access to endpoints aligns with growing zero-trust network strategies.
- SME Market Expansion: Small and medium businesses seek affordable, scalable endpoint protection solutions.
- Mobile Device Security: Rising mobile usage creates opportunities for specialized endpoint protection solutions.
Endpoint Security Market Report Segmentation Analysis
The endpoint security market is categorized into distinct segments to understand its structure, growth prospects, and emerging trends. Below is the standard segmentation approach used in industry reports:
By Component:
- Solution: Software tools such as antivirus, anti-malware, firewall, and EDR that protect endpoints from threats.
- Services: Professional offerings such as consulting, implementation, monitoring, and managed endpoint security support.
By Organization Size:
- Large Enterprises: Implement advanced, multi-layered endpoint security solutions to safeguard extensive global IT infrastructure.
- SMEs: Adopt cost-effective, scalable endpoint security solutions suited for smaller, simpler IT environments.
By Industry Vertical:
- BFSI
- IT and Telecom
- Government
- Healthcare
- Manufacturing
- Retail and E-commerce
- Others
By Geography:
- North America
- Europe
- Asia Pacific
- South & Central America
- Middle East & Africa
Endpoint Security Market Report Scope
| Report Attribute | Details |
|---|---|
| Market size in 2024 | US$ 58.22 Billion |
| Market Size by 2031 | US$ 144.95 Billion |
| Global CAGR (2025 - 2031) | 14.2% |
| Historical Data | 2021-2023 |
| Forecast period | 2025-2031 |
| Segments Covered |
By Component
|
| Regions and Countries Covered |
North America
|
| Market leaders and key company profiles |
|
Endpoint Security Market Players Density: Understanding Its Impact on Business Dynamics
The Endpoint Security Market is growing rapidly, driven by increasing end-user demand due to factors such as evolving consumer preferences, technological advancements, and greater awareness of the product's benefits. As demand rises, businesses are expanding their offerings, innovating to meet consumer needs, and capitalizing on emerging trends, which further fuels market growth.
Endpoint Security Market Share Analysis by Geography
The endpoint security market in North America is experiencing rapid growth driven by increasing cyber threats, expanding remote work, and surging adoption of advanced security solutions across enterprises. Emerging markets in South & Central America, the Middle East, and Africa present untapped opportunities for network security, enabling businesses to adopt advanced endpoint protection and managed security solutions.
The endpoint security market growth differs in each region due to variations in cyber threat levels, IT infrastructure maturity, regulatory frameworks, and technology adoption rates. Below is a summary of market share and trends by region:
1. North America
- Market Share: Holds a significant portion of the global market
- Key Drivers:
- Rising cyber threats High frequency of ransomware and phishing attacks drives robust endpoint security adoption.
- Remote work adoption
- Stringent regulatory compliance
- Trends: Increased adoption of AI-driven endpoint detection and response (EDR).
2. Europe
- Market Share: Substantial share owing to early, stringent EU regulations
- Key Drivers:
- GDPR and data protection regulations. Businesses must comply with strict data privacy laws.
- Growing cloud adoption
- Increased use of IoT devices.
- Trends: Integration of zero-trust security models across enterprises.
3. Asia Pacific
- Market Share: Fastest-growing region with dominant market share
- Key Drivers:
- Rapid digitalization. The expanding IT infrastructure increases vulnerability to cyberattacks
- Growing SME adoption of IT solutions
- Rising cybercrime and ransomware incidents
- Trends: AI and machine learning-based threat detection are gaining traction.
4. Middle East and Africa
- Market Share: Although small, it is growing quickly
- Key Drivers:
- Increasing cyberattacks on critical infrastructure. Governments and enterprises prioritize endpoint protection.
- Growing cloud services adoption
- Regulatory initiatives for cybersecurity
- Trends: Expansion of managed security services to address talent shortages.
5. South & Central America
- Market Share: Growing market with steady progress
- Key Drivers:
- Rising digital transformation. Businesses adopting online platforms face higher cyber risks.
- Low cybersecurity awareness among SMEs.
- Increasing mobile and remote workforce
- Trends: Growth in cloud-based and managed endpoint security solutions.
Endpoint Security Market Players Density: Understanding Its Impact on Business Dynamics
High Market Density and Competition
Competition is intense due to the presence of major global players such as Oracle Corp, International Business Machines Corp, Open Text Corp, SAP SE, Cisco Systems Inc, Microsoft Corp, Broadcom Inc, Palo Alto Networks Inc, CrowdStrike Holdings Inc, and Fortinet Inc.
This high level of competition urges companies to stand out by offering:
- Innovative products and services
- Advanced Threat Detection
- AI-driven threat detection
- Seamless integration
- Cost-effective, scalable options.
Opportunities and Strategic Moves
- AI and ML integration: Develop predictive and automated threat detection solutions.
- Customer-Centric Offerings: Provide flexible pricing, easy deployment, and regulatory compliance.
Disclaimer: The companies listed above are not ranked in any particular order.
Other companies analyzed during the course of research:
- VMware Carbon Black
- VIPRE Security Group
- Kaspersky Lab
- Absolute Software
- Cynet
- Trend Micro
- SentinelOne
- Bitdefender
- ESET
- Webroot
Endpoint Security Market News and Recent Developments
- CrowdStrike announced CrowdStrike Falcon Next-Gen Identity Security, the first unified solution to protect every identity, August 2025 - CrowdStrike announced CrowdStrike Falcon Next-Gen Identity Security, the first unified solution to protect identity—human, non-human, and AI agent—across the full hybrid identity lifecycle and every environment. Delivered today, without delays or integration complexity through the AI-native CrowdStrike Falcon platform, the new offering protects identities across on-premises, cloud, SaaS, and workloads, removing security blind spots and replacing fragmented controls. CrowdStrike unifies initial access prevention, modern privileged access management (PAM), identity threat detection and response (ITDR), SaaS identity security, and agentic identity protection to stop identity-driven breaches across domains.
- EVOTEK has partnered with Sysense (ASPM). April 2023 - EVOTEK has partnered with Sysense, a leading provider of Unified Security and Endpoint Management (USEM) solutions, to offer customers a comprehensive suite of endpoint management and security services. Through this collaboration, EVOTEK will leverage Sysense’s robust solutions—including Sysense Secure, Sysense Manage, and Sysense Enterprise—to enhance endpoint management capabilities and provide stronger, more reliable security for its clients.
Endpoint Security Market Report Coverage and Deliverables
The "Endpoint Security Market Size and Forecast (2021–2031)" report provides a detailed analysis of the market covering below areas:
- Endpoint Security Market size and forecast at global, regional, and country levels for all the key market segments covered under the scope
- Endpoint Security Market trends, as well as market dynamics such as drivers, restraints, and key opportunities
- Detailed PEST and SWOT analysis
- Endpoint Security Market For Healthcare analysis covering key market trends, global and regional framework, major players, regulations, and recent market developments
- Industry landscape and competition analysis covering market concentration, heat map analysis, prominent players, and recent developments for the endpoint security market
- Detailed company profiles
Frequently Asked Questions
Ankita is a dynamic market research and consulting professional with over 8 years of experience across the technology, media, ICT, and electronics & semiconductor sectors. She has successfully led and delivered 100+ consulting and research assignments for global clients such as Microsoft, Oracle, NEC Corporation, SAP, KPMG, and Expeditors International. Her core competencies include market assessment, data analysis, forecasting, strategy formulation, competitive intelligence, and report writing.
Ankita is adept at handling complete project cycles—from pre-sales proposal design and client discussions to post-sales delivery of actionable insights. She is skilled in managing cross-functional teams, structuring complex research modules, and aligning solutions with client-specific business goals. Her excellent communication, leadership, and presentation abilities have enabled her to consistently deliver value-driven outcomes in fast-paced and evolving market environments.
- Historical Analysis (2 Years), Base Year, Forecast (7 Years) with CAGR
- PEST and SWOT Analysis
- Market Size Value / Volume - Global, Regional, Country
- Industry and Competitive Landscape
- Excel Dataset
Testimonials
The Insight Partners' SCADA System Market report is comprehensive, with valuable insights on current trends and future forecasts. The team was highly professional, responsive, and supportive throughout. We are very satisfied and highly recommend their services.
RAN KEDEM Partner, Reali Technologies LTDsI requested a report on a very specific software market and the team produced the report in a few days. The information was very relevant and well presented. I then requested some changes and additions to the report. The team was again very responsive and I got the final report in less than a week.
JEAN-HERVE JENN Chairman, Future AnalyticaWe worked with The Insight Partners for an important market study and forecast. They gave us clear insights into opportunities and risks, which helped shape our plans. Their research was easy to use and based on solid data. It helped us make smart, confident decisions. We highly recommend them.
PIYUSH NAGPAL Sr. Vice President, High Beam GlobalThe Insight Partners delivered insightful, well-structured market research with strong domain expertise. Their team was professional and responsive throughout. The user-friendly website made accessing industry reports seamless. We highly recommend them for reliable, high-quality research services
YUKIHIKO ADACHI CEO, Deep Blue, LLC.This is the first time I have purchased a market report from The Insight Partners.While I was unsure at first, I visited their web site and felt more comfortable to take the risk and purchase a market report.I am completely satisfied with the quality of the report and customer service. I had several questions and comments with the initial report, but after a couple of dialogs over email with their analyst I believe I have a report that I can use as input to our strategic planning process.Thank you so much for taking the extra time and making this a positive experience.I will definitely recommend your service to others and you will be my first call when we need further market data.
JOHN SUZUKI President and Chief Executive Officer, Board Director, BK TechnologiesI wish to appreciate your support and the professionalism you displayed in the course of attending to my request for information regarding to infectious disease IVD market in Nigeria. I appreciate your patience, your guidance, and the fact that you were willing to offer a discount, which eventually made it possible for us to close a deal. I look forward to engaging The Insight Partners in the future, all thanks to the impression you have created in me as a result of this first encounter.
DR CHIJIOKE ONYIA MANAGING DIRECTOR, PineCrest Healthcare Ltd.Reason to Buy
- Informed Decision-Making
- Understanding Market Dynamics
- Competitive Analysis
- Identifying Emerging Markets
- Customer Insights
- Market Forecasts
- Risk Mitigation
- Boosting Operational Efficiency
- Strategic Planning
- Investment Justification
- Tracking Industry Innovations
- Aligning with Regulatory Trends





 Get Free Sample For
Get Free Sample For